[ad_1]
There are 3 components of cybersecurity. In case you’re lacking any
considered one of them, you can be making your self an easy target for knowledge thieves
and sure buying a one-way ticket to a world of harm.
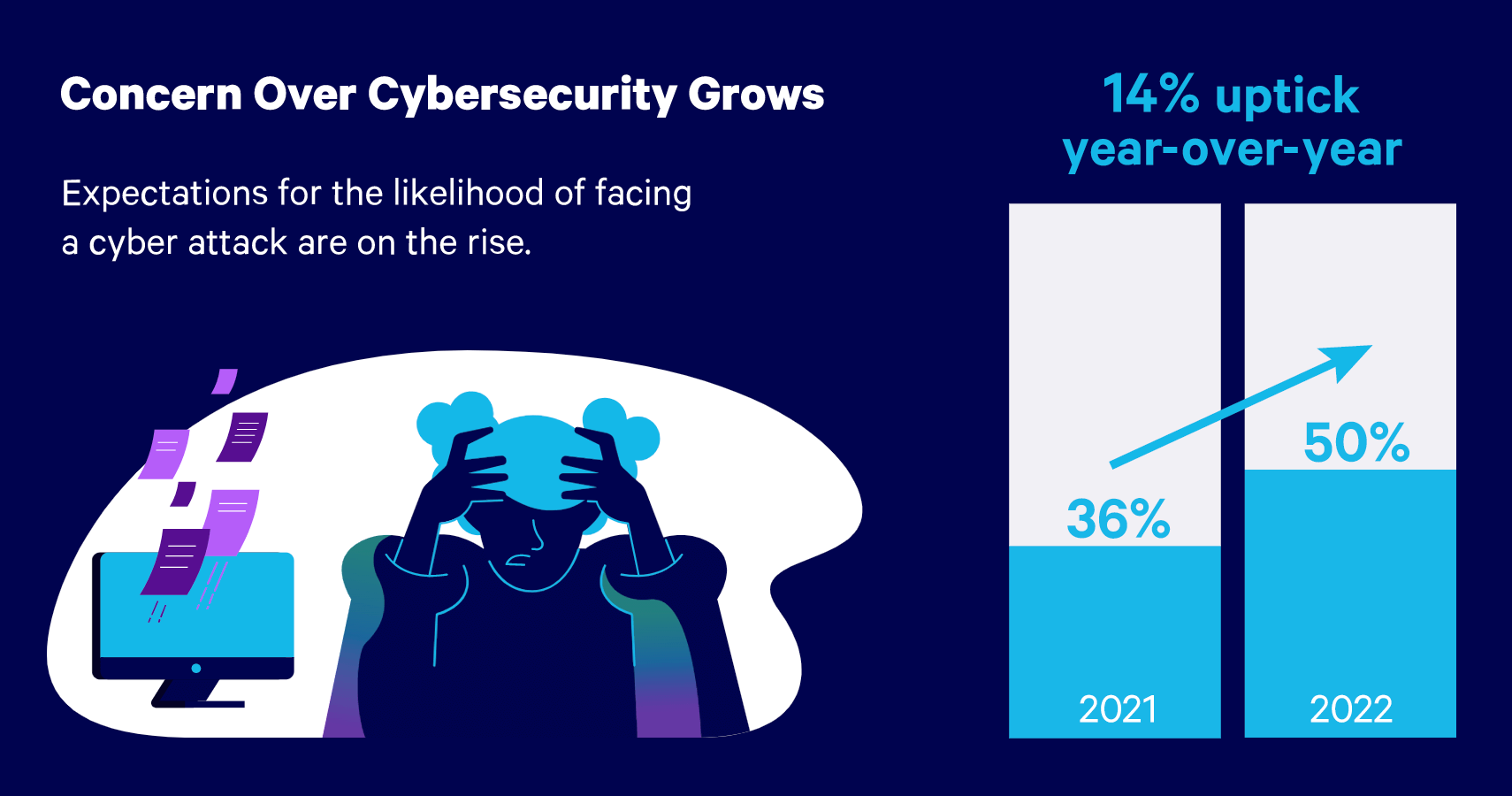
You may be questioning if that is one thing you actually want to fret about. Properly, Embroker requested enterprise house owners that precise factor. Of their latest Cyber Threat Index Report, founders in 2022 admitted that they have been way more anxious about cyber assaults than they have been within the earlier 12 months.
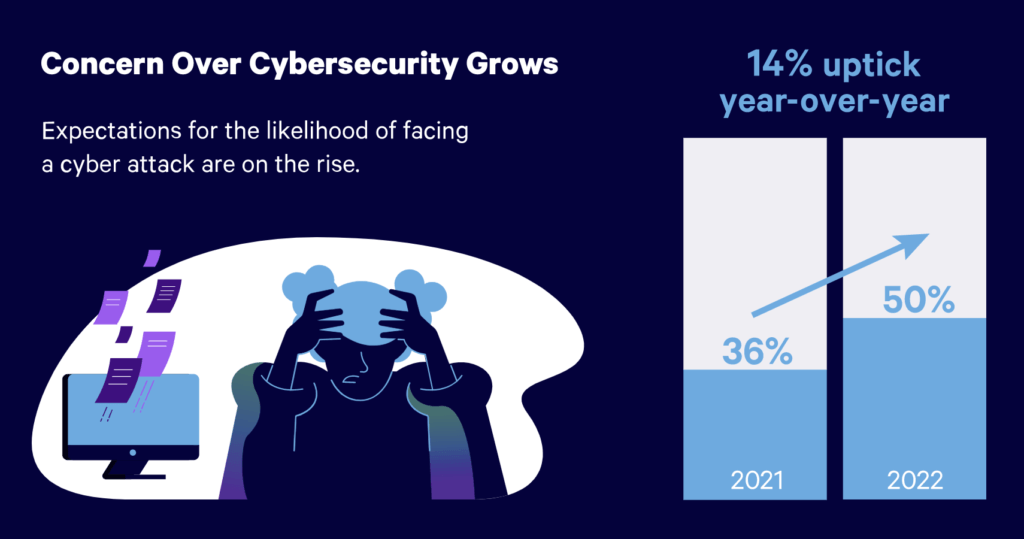
Check out the full report for more details.
The three components of cybersecurity are prevention, detection, and response. Inside every of
these are particular steps it is advisable take to offer your self the most effective likelihood of
foiling cybercriminals who need your knowledge—particularly, your shopper’s names,
addresses, Social Safety numbers, checking account particulars, taxpayer
data, and varied different secrets and techniques, together with confidential
correspondences, statements in opposition to curiosity, and your pre-trial technique
notes.
These are knowledge you will have an obligation to safeguard, and breaching that obligation
carries with it some disagreeable penalties. For instance, it might value you
a ton of cash to pay out to injured shoppers. It might value you your fame
since a knowledge breach isn’t something you'll be able to conceal—when it occurs, you will have
an ethical obligation and virtually certainly a statutory one as nicely to publicly
disclose that confidential knowledge entrusted to you will have been compromised.
And a breach of the obligation to safeguard shopper data as outlined in Rule
1.6(c) of the American Bar Affiliation’s Mannequin Guidelines of Skilled
Accountability might value you your legislation license, both briefly or
completely.
So, with out additional fanfare, let’s have a look at the three elements of
cybersecurity. We start with arguably crucial of the three components of cybersecurity: the aspect of prevention.
The three Parts of Cybersecurity: Prevention
With regards to cybersecurity, the previous saying about an oz of prevention
being value a pound of treatment is completely true. Certainly, probably the most cost-
efficient (and sanity-sparing) manner of saving your self from the results
of a cyberattack shouldn't be permitting it to happen.
Right here’s what it is best to do if you wish to stop a cyberattack.
The primary order of enterprise—and that is super-important, which is why I’m
telling you about it proper up entrance—procure a cyber-insurance coverage. Don't
depend on another type of insurance coverage to protect yourself from the
penalties of a cyberattack. Cyber insurance is the one sort of protection
that may maintain you from going below financially due to a knowledge breach.
Granted, this insurance coverage received’t cease hackers and different malefactors from
efficiently dipping their sticky fingers into your jar of honey-sweet knowledge,
however it’s an important safety measure, nonetheless.
Subsequent, get within the behavior of being stingy with the quantity of data you
share on-line. The much less you share, the higher since you by no means know who
may lurk within the digital shadows to spy in your e mail exchanges and
web site visits. Say “no thanks” when the little popup in your display screen invitations
you to share location knowledge. Decline the supply to just accept cookies, if doable.
Continuously run safety scans of your programs. Guarantee your pc’s
working system, browsers, packages, and every part else is updated.
Which means it is advisable have the newest model of every put in. You additionally
ought to have the latest safety patches in place. Cobwebbed software program is
normally a critical vulnerability.
From there, apply a scrutinizing eye to all of your passwords. In case you’re utilizing
weak passwords, cease. Swap them out for brand new and powerful passwords. A weak
password is one thing alongside the traces of 123456. A robust password
comprises a randomized mixture of upper- and lower-case letters plus numerals
and particular characters. Your greatest guess is to amass a password administration
app—it’ll routinely create hyper-strong passwords, and no two will ever
be the identical. The password supervisor may even bear in mind each for you,
so that you’ll by no means want to jot down them down. Yet one more factor: activate multi-
issue authentication (MFA), which would require you to supply not less than one
further piece of proof to show you might be who you declare to be (and never
some hacker who managed to pilfer your password) earlier than it'll roll out the
welcome mat and grant you entry.
Begin utilizing a digital non-public community (VPN) everytime you hop onto the
web, whether or not to ship an e mail or go to an internet site. Backup your recordsdata
regularly: as soon as a day is nice, as soon as a minute is right (there are safety
packages you'll be able to acquire that may routinely backup your recordsdata for you
and, as a bonus, encrypt them—encryption being an excellent technique to
frustrate cybercriminals).
Lastly, to actually get a grasp of how one can stop a cyber assault (in addition to the three components of cybersecurity) join cybersecurity coaching—not only for your self however everybody
in your workplace. With coaching, you'll discover ways to spot phishing scams, e mail
compromise assaults, and different types of trickery designed to lull you into
giving freely your entry credentials or unwittingly initiating a lethal
obtain of viruses or malware. Coaching may even instill in you and your
group quite a few good habits, akin to not sharing private passwords and
by no means leaving the desk with out first locking the pc display screen.
The three Parts of Cybersecurity: Detection
Cyberthieves are so good at what they try this it sometimes takes the sufferer
200 days to understand a knowledge breach has occurred. It takes that lengthy as a result of
the common sufferer isn’t sufficiently vigilant in watching out for the indicators of a
cyberattack.
Due to this fact, it is best to evaluation your financial institution and bank card statements recurrently.
Additionally, take a extra frequent have a look at what the credit score bureaus (Equifax,
TransUnion, and Experian) are saying about you—for instance, are they
reporting that you simply’ve taken out a mortgage you realize nothing about or have
moved to a brand new deal with in a location you’ve by no means a lot as visited?
These are indicators you’ve been knowledge breached.
Pay nearer consideration to how your computer systems and cellular gadgets are
behaving. Be suspicious in the event that they’re out of the blue working sluggish or doing
inexplicable bizarre issues—likelihood is they’re contaminated with viruses or
malware, or maybe a hacker has burrowed in and brought management.
One other signal of a cyberattack is that you simply’ll begin to obtain emails seemingly
from colleagues and others with whom you will have a trusted relationship.
These emails will seem genuine however are literally from cybercrooks doing a
actually good impersonation of your colleague. The giveaway that they’re
frauds is that you simply’ll be requested to share your login credentials with them or to
pay this bill for one thing you realize you paid months in the past.
The three Parts of Cybersecurity: Response
The quicker you shift into response mode after a cyberattack is detected, the
higher off you'll be. It should assist when you took time through the prevention part
to create an motion plan detailing your response so that you simply and your group
know precisely what to do and through which order. No guessing, no working round
along with your hair on fireplace.
Within the occasion of a breach, instantly contact your cyber-insurance firm
to allow them to start coming to your help with the money and different help you
might want to keep away from monetary and reputational destroy.

Trade-leading safety to your tech firm.
Get the correct protection at the most effective worth.
This subsequent step, some say, must be carried out earlier than you contact your
cyber-insurance firm, whereas others say to do it proper after. Both manner,
it is advisable seal off your programs from the surface world in order that no additional
knowledge loss can happen. Which means chopping your web connections and killing
your community feed. Please don’t return on-line till a pc safety
specialist or IT-managed service supplier sift via your programs with a
fine-tooth comb to find out the way you have been breached after which plug that
gap.
Then it's essential to start the method of notifying all affected events—first and
foremost, your shoppers. It's important to inform them that you simply have been the sufferer of a
knowledge breach and clarify how that occasion impacts them. It’s a wise transfer to
embody in that notification a promise to pay for credit score monitoring in order that
these impacted by the breach might be well timed alerted if their stolen private
data is subsequently used to have interaction in monetary crimes.
The remaining is fairly easy. Contact legislation enforcement to allow them to know
what occurred. Ditto Social Safety, your financial institution, and your collectors in order that they
can put holds in your accounts and subject new ones.
And there you will have it. The three components of cybersecurity; are
prevention, detection, and response. You want all three in place in order for you
to come back out on the opposite aspect of a knowledge breach, a phishing rip-off, a
ransomware attack, or the rest cyber-based along with your funds, shopper
roster, model fame, and probably even your legislation license intact.

Is cyber danger on the rise?
Learn our 2022 Cyber Threat Index Report to search out out what companies are anxious about, how they’re defending themselves, and what the longer term holds.

Tom Lambotte
CEO of Boba Guard
This text was offered by Tom Lambotte, a cybersecurity skilled who has been within the tech help trade for over a decade. Tom based BobaGuard in 2019, which provides turnkey options to solo attorneys and small-to-medium legislation corporations. As well as, Tom can also be the CEO and Founding father of GlobalMac IT, a longtime managed service supplier specializing in serving attorneys nationwide who use Macs by implementing his Confirmed Course of™.
[ad_2]